الدورات
title
Cybercriminals Exploit Popular Game Engine Godot to Distribute Cross-Platform Malware
A popular open-source game engine, Godot Engine, is being exploited by cybercriminals in a new malware campaign, GodLoader, which has infected over 17,000 systems since at least June 2024.
Check Point, in a recent analysis, reported that cybercriminals have been taking advantage of Godot Engine's capabilities to execute malicious GDScript code. This code triggers harmful commands and distributes malware. What's alarming is that this technique is undetected by nearly all antivirus engines on VirusTotal.
The engine’s multi-platform support makes it an attractive tool for attackers. Cybercriminals are leveraging this flexibility to target devices across various operating systems, expanding the attack surface and allowing malware to spread on a larger scale.
Eli Smadja, the Security Research Group Manager at Check Point, stated, "The Godot Engine’s flexibility has made it a target for cybercriminals, enabling stealthy, cross-platform malware like GodLoader to spread rapidly by exploiting trust in open-source platforms. For the 1.2 million users of Godot-developed games, the implications are profound—not just for their devices, but for the integrity of the
gaming ecosystem itself."
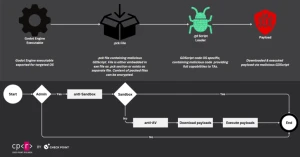
Exploiting GitHub for Distribution
The campaign’s uniqueness lies in its use of the Stargazers Ghost Network, a network of around 200 GitHub repositories and more than 225 fake accounts that distribute GodLoader.
These fake accounts have been starring malicious repositories, making them appear legitimate and safe to unsuspecting users. The repositories were released in four waves, primarily targeting developers, gamers, and general users.
The malware is distributed via Godot Engine executables, also known as .PCK files. These files drop the loader malware, which is then responsible for downloading and executing payloads, including the RedLine Stealer and the XMRig cryptocurrency miner from a Bitbucket repository.
The loader has features designed to bypass detection in sandboxed and virtual environments, including adding the *C:* drive to the Microsoft Defender Antivirus exclusions list, thus preventing detection of the malware.
Cross-Platform Impact
While the malware primarily targets Windows machines, it can easily be adapted to infect macOS and Linux systems. The attackers are currently building custom Godot Engine executables to propagate the malware, but this technique could be further escalated by tampering with a legitimate Godot-built game if the attacker obtains the symmetric encryption key used to extract the .PCK file.
This type of attack could be mitigated by switching to an asymmetric-key encryption algorithm, which uses a public-private key pair for encryption and decryption.
A Wake-Up Call for the Industry
This campaign serves as another reminder that attackers often exploit legitimate platforms and services to evade security measures. It highlights the need for users to download software only from trusted sources.
Check Point remarked, "Threat actors have utilized Godot's scripting capabilities to create custom loaders that remain undetected by many conventional security solutions. Since Godot's architecture allows platform-agnostic payload delivery, attackers can easily deploy malicious code across Windows, Linux, macOS, and potentially Android."
By combining targeted distribution methods with a stealthy, undetected technique, the attackers have achieved exceptionally high infection rates. This cross-platform approach enhances the malware's versatility, enabling it to affect multiple operating systems and giving cybercriminals a powerful tool to target various devices.
As defenders continue to build new security measures, it is no surprise that cybercriminals will keep seeking out new tools and techniques to bypass detection and deliver malware. Godot Engine, with its widespread use and cross-platform capabilities, is the latest tool in their arsenal.